Cybersecurity has undergone a fundamental transformation over the past decade. What was once a domain dominated by firewalls, antivirus systems, and perimeter defenses has now evolved into a strategic discipline deeply embedded in organizational governance. Today, cybersecurity is not just about preventing attacks—it is about ensuring resilience, accountability, compliance, and intelligent decision-making across the enterprise.
Modern organizations operate in an increasingly complex digital ecosystem driven by cloud computing, remote work, interconnected systems, and data-driven technologies. In this environment, cybersecurity must extend beyond technical controls to include structured governance practices. This is where Governance, Risk, and Compliance (GRC) plays a critical role.
At the heart of effective cybersecurity governance lie four essential competencies: policy and documentation analysis, compliance framework knowledge, risk assessment and control mapping, and AI training data validation combined with analytical reasoning. Together, these capabilities enable organizations to build secure, compliant, and adaptive security programs.
This article explores how these components function in practice and why they are indispensable in modern cybersecurity operations.
The Foundation: Policy and Documentation Analysis
Security documentation forms the backbone of any mature cybersecurity program. Without clearly defined policies and structured documentation, even the most advanced security technologies can fail due to inconsistency, misconfiguration, or lack of accountability.
At its core, documentation provides clarity. It defines expectations, standardizes processes, and ensures that all stakeholders—from technical teams to executive leadership—are aligned in their understanding of security practices.
Security documentation typically follows a hierarchical structure consisting of policies, standards, procedures, and controls.
Security Policies: Defining Strategic Intent
Security policies represent the highest level of documentation within an organization. These are formal statements issued by management that define the organization’s security objectives, guiding principles, and expectations.
Policies answer a fundamental question: What must be achieved?
For example, a policy might state that all sensitive data must be encrypted during storage and transmission. While this does not specify how encryption should be implemented, it establishes a non-negotiable requirement that guides all subsequent security decisions.
Policies are critical because they:
- Establish organizational commitment to security
- Align security objectives with business goals
- Provide a foundation for compliance and audits
Without strong policies, organizations often struggle with fragmented security efforts and unclear responsibilities.
Security Standards: Translating Intent into Requirements
While policies define objectives, standards translate those objectives into measurable technical requirements. They answer the question: What specific rules must be followed?
For instance, if a policy mandates encryption, a standard may specify the use of AES-256 for data at rest and TLS 1.2 or higher for data in transit.
Standards ensure consistency across systems and teams. They eliminate ambiguity and provide clear benchmarks for implementation and evaluation.
Procedures: Operationalizing Security
Procedures take standards one step further by providing detailed, step-by-step instructions for executing security tasks. They answer the question: How is the task performed?
For example, a user access provisioning procedure might include identity verification, role-based access assignment, multi-factor authentication setup, and logging configuration.
Procedures are essential for operational efficiency. They ensure that tasks are performed consistently regardless of who executes them, reducing the risk of human error.
Security Controls: Enforcing and Validating
Controls are the mechanisms that enforce policies and standards. They can be technical, administrative, or physical in nature.
Examples include:
- Access control systems
- Encryption mechanisms
- Endpoint detection and response tools
- Security monitoring platforms
Controls are typically categorized into preventive, detective, and corrective types. Effective policy analysis involves evaluating whether these controls adequately support the organization’s policies and standards.
In practice, this means asking critical questions:
- Do existing controls fully enforce policy requirements?
- Are there gaps between documented standards and actual implementation?
- Are controls effective in real-world scenarios?
This analytical approach transforms documentation from a static artifact into a dynamic governance tool.
The Role of Compliance Frameworks in Cybersecurity Governance
In today’s regulatory environment, organizations cannot rely solely on internally defined security practices. They must align with established compliance frameworks that provide standardized approaches to managing cybersecurity risks.
Compliance frameworks serve as structured guidelines that help organizations design, implement, and evaluate their security programs. They also play a crucial role in demonstrating accountability to regulators, customers, and stakeholders.
SOC 2: Evidence-Based Security Assurance
SOC 2 is widely used by cloud service providers and SaaS organizations. It focuses on five trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
One of the defining characteristics of SOC 2 is its emphasis on evidence. Organizations must not only implement controls but also demonstrate that those controls are consistently operating over time.
This requires:
- Detailed documentation
- Continuous monitoring
- Audit-ready processes
SOC 2 shifts cybersecurity from a theoretical exercise to a measurable, verifiable practice.
ISO 27001: Building a Structured ISMS
ISO 27001 provides a comprehensive framework for establishing an Information Security Management System (ISMS). It emphasizes a risk-based approach, meaning that security controls are selected and implemented based on identified risks.
Key elements include:
- Risk assessment and treatment
- Policy development
- Asset management
- Continuous improvement
ISO 27001 encourages organizations to think strategically about security rather than adopting a one-size-fits-all approach.
NIST Cybersecurity Framework: Operational Flexibility
The NIST Cybersecurity Framework offers a flexible, outcome-based approach to managing cybersecurity risk. It organizes security activities into five core functions: Identify, Protect, Detect, Respond, and Recover.
Unlike certification-based frameworks, NIST is designed for adaptability. Organizations can tailor it to their specific needs, making it particularly valuable for dynamic environments.
Together, these frameworks provide a structured yet flexible foundation for cybersecurity governance. Professionals who understand how to interpret and apply these frameworks are highly valuable in modern organizations.
Risk Assessment and Control Mapping: The Core of Decision-Making
Risk assessment is the process that connects governance with action. It enables organizations to identify potential threats, evaluate vulnerabilities, and prioritize security investments.
Without risk assessment, security efforts often become reactive and inefficient.
The Risk Assessment Process
A comprehensive risk assessment involves several key steps:
Asset Identification
Organizations must first identify their critical assets. These may include customer data, intellectual property, financial systems, and cloud infrastructure.
Understanding what needs to be protected is the foundation of all security efforts.
Threat Identification
Next, organizations identify potential threats such as malware attacks, insider threats, data breaches, and supply chain risks.
This step requires awareness of both current threat landscapes and emerging attack vectors.
Vulnerability Analysis
Vulnerabilities represent weaknesses that could be exploited by threats. These may include unpatched systems, weak access controls, or misconfigured cloud environments.
Regular vulnerability assessments are essential for maintaining a strong security posture.
Risk Evaluation
Risk is typically calculated as the product of likelihood and impact. This helps organizations prioritize which risks require immediate attention.
High-impact, high-likelihood risks demand urgent mitigation, while lower-risk issues can be addressed over time.
Control Mapping: Bridging Risk and Compliance
Control mapping is the process of aligning security controls with both identified risks and compliance requirements.
For example:
- A risk of unauthorized access may be mitigated through multi-factor authentication, mapped to access control requirements in standards.
- A risk of data leakage may be addressed through encryption, aligned with confidentiality requirements.
Control mapping is critical during audits because it demonstrates how security measures address both business risks and regulatory expectations.
It also provides clarity by linking abstract risks to concrete actions.
The Emerging Role of AI Training Data Validation
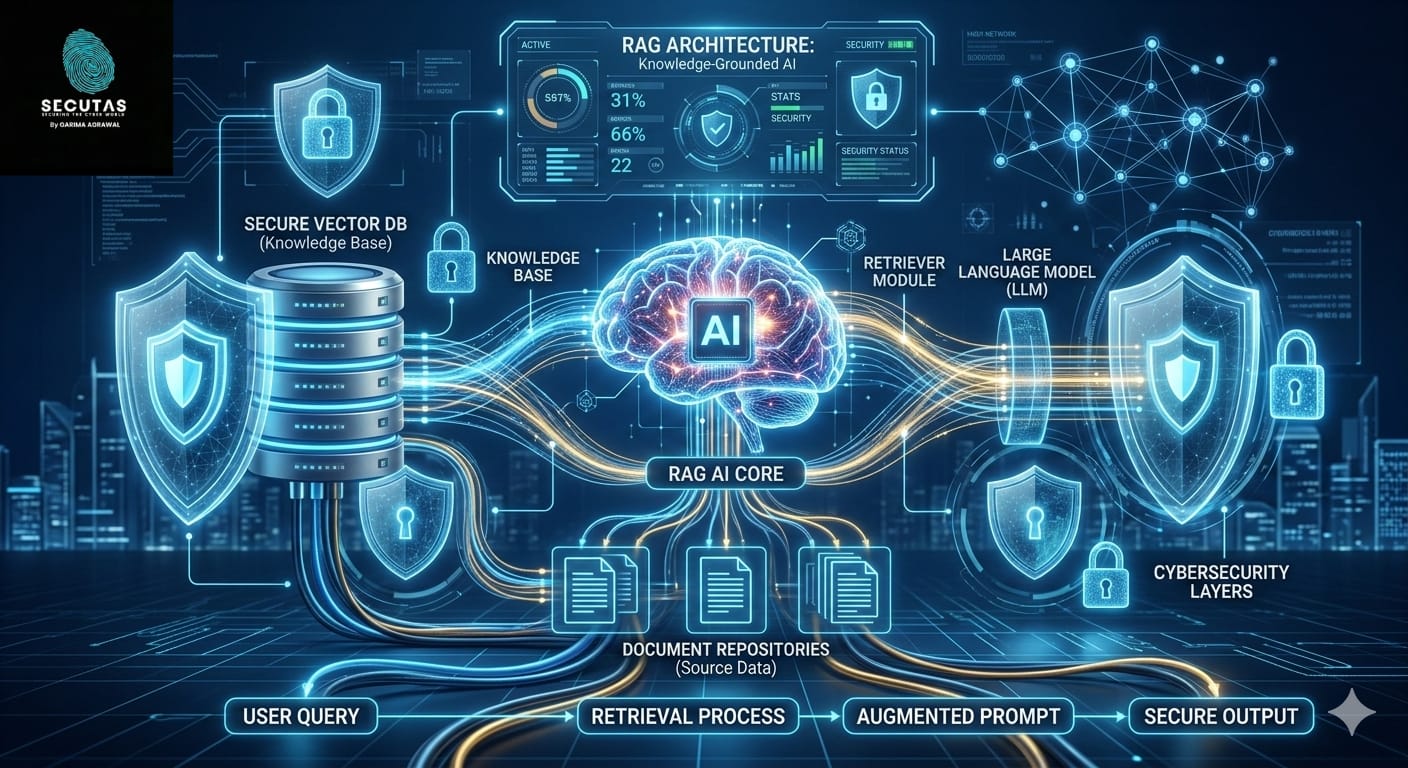
Artificial intelligence is rapidly becoming a cornerstone of cybersecurity. From threat detection to behavioral analytics, AI systems are enabling faster and more accurate responses to security incidents.
However, the effectiveness of AI depends entirely on the quality of the data used to train it.
Why AI Data Validation Matters
Poorly validated data can introduce significant risks:
- Biased decision-making
- Inaccurate threat detection
- Increased false positives and false negatives
- Vulnerability to model poisoning attacks
For example, if a machine learning model is trained on incomplete or outdated attack data, it may fail to detect new forms of malware.
This highlights a critical reality: AI is not inherently secure—it must be governed and validated.
Key Validation Techniques
Data Integrity Verification
Ensuring that training data is authentic and unaltered is fundamental. Techniques such as hash verification and secure data pipelines help maintain data integrity.
Bias Detection
Bias in datasets can lead to unfair or inaccurate outcomes. Security teams must analyze datasets to ensure they are balanced and representative.
Adversarial Testing
Attackers may attempt to manipulate AI models by injecting malicious data. Adversarial testing simulates such scenarios to evaluate model resilience.
Continuous Monitoring
AI models are not static. Their performance can degrade over time due to changes in data patterns. Continuous monitoring helps detect performance drift and maintain accuracy.
AI validation introduces a new dimension to cybersecurity governance—one that requires both technical expertise and analytical rigor.
Analytical Reasoning: The Human Intelligence Behind Security
While automation and AI play an increasing role in cybersecurity, human analytical reasoning remains indispensable.
Security professionals must interpret complex datasets, identify patterns, and make informed decisions under uncertainty.
This includes analyzing:
- Security logs
- Risk reports
- Compliance documentation
- AI-generated insights
Analytical reasoning enables professionals to:
- Detect subtle anomalies
- Prioritize responses effectively
- Evaluate the effectiveness of controls
- Make strategic decisions
In many ways, analytical reasoning is the bridge between data and action.
Why These Skills Are Critical for Modern Cybersecurity Careers
The cybersecurity landscape is evolving rapidly due to several key factors:
- Expansion of cloud computing
- Integration of artificial intelligence
- Increasing regulatory requirements
- Sophistication of cyber threats
As a result, organizations are seeking professionals who can go beyond technical implementation and contribute to governance and strategy.
Roles that benefit from these skills include:
- GRC Analyst
- Security Compliance Specialist
- Risk Analyst
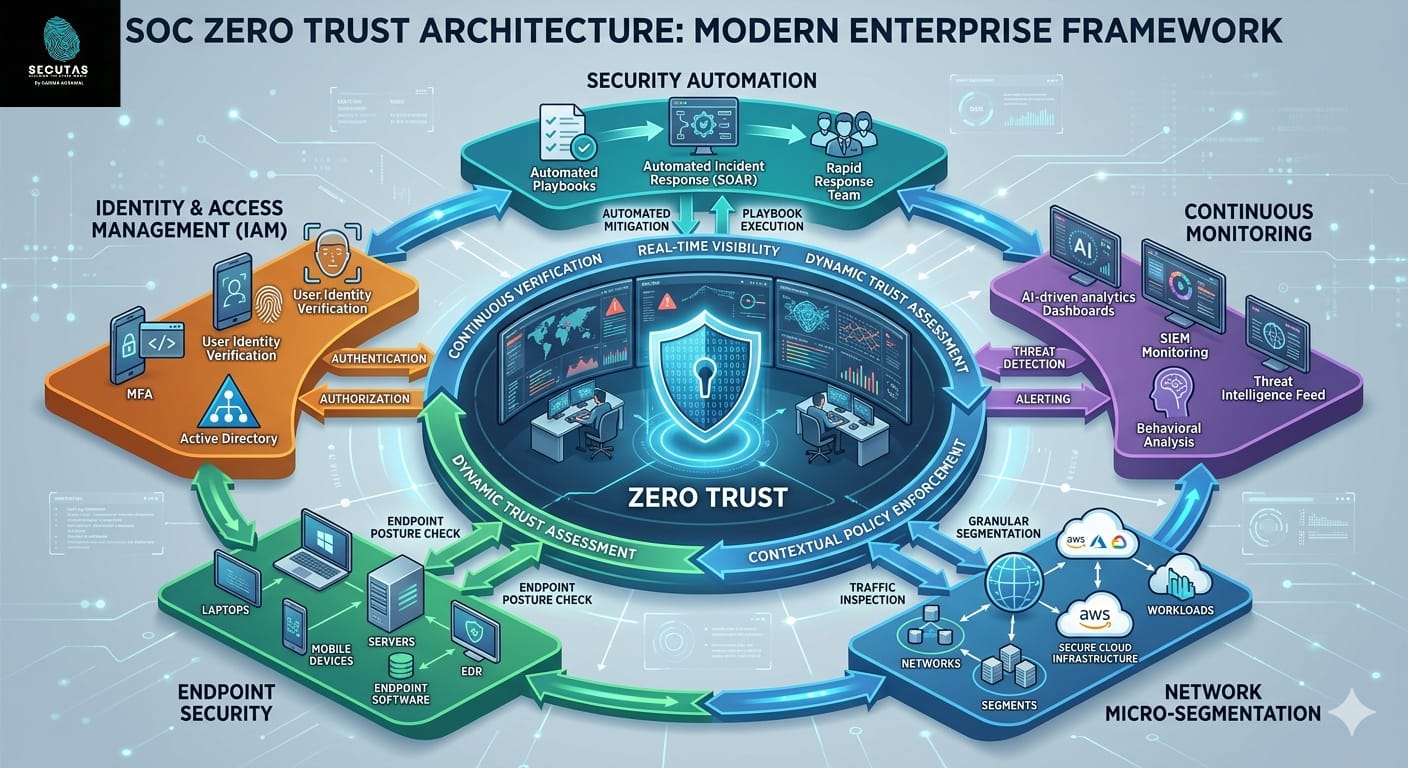
- SOC Analyst
- AI Security Researcher
These roles require a combination of technical knowledge, business understanding, and analytical thinking.
Professionals who can navigate policies, interpret frameworks, assess risks, and validate AI systems are uniquely positioned to lead in this evolving landscape.
Building a Holistic Cybersecurity Strategy
Effective cybersecurity governance is not achieved through isolated efforts. It requires integration across multiple domains.
Policy analysis ensures that expectations are clearly defined and aligned with organizational goals.
Compliance frameworks provide structured guidance and standardization.
Risk assessment enables prioritization and informed decision-making.
AI validation ensures that advanced technologies operate reliably and securely.
When these elements work together, organizations can build a comprehensive security strategy that is both resilient and adaptive.
Final Thoughts
Cybersecurity is no longer just a technical discipline—it is a strategic function that supports organizational resilience and trust.
Modern security programs must be built on a foundation of governance, documentation, compliance, and intelligent analysis. Policy analysis ensures clarity, compliance frameworks provide structure, risk assessment drives prioritization, and AI validation safeguards emerging technologies.
Together, these competencies form the backbone of effective cybersecurity governance.
For professionals entering or advancing in the field, mastering these areas is not just beneficial—it is essential. As organizations continue to navigate an increasingly complex digital landscape, the demand for governance-focused cybersecurity expertise will only continue to grow.
Those who invest in developing these skills will not only enhance their career prospects but also play a critical role in shaping the future of cybersecurity.


Leave a Reply