SOC Zero Trust Architecture: A Modern Framework for Securing Cybersecurity Operations
Abstract
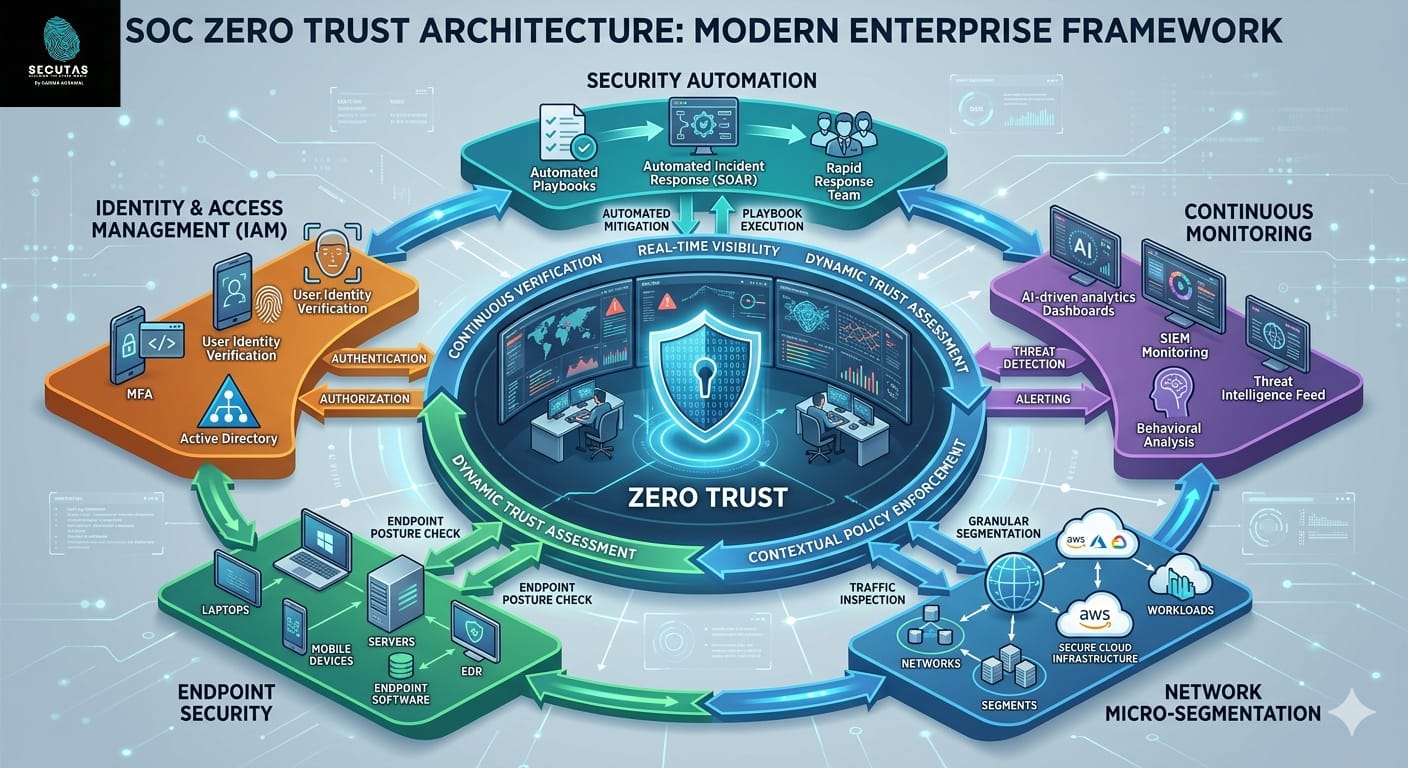
Modern enterprises face increasingly sophisticated cyber threats that bypass traditional security perimeters. The widespread adoption of cloud computing, remote work environments, mobile devices, and interconnected digital infrastructures has significantly expanded the attack surface for organizations. As a result, traditional perimeter-based security models are no longer sufficient for protecting critical assets and sensitive data. Zero Trust Architecture (ZTA) has emerged as a transformative cybersecurity framework designed to address these challenges by eliminating implicit trust and continuously verifying every access request. This research article explores the concept of Security Operations Center (SOC) Zero Trust Architecture, its core principles, components, implementation strategies, and its role in strengthening organizational cybersecurity posture. The study also examines how modern SOC environments integrate identity management, device verification, network segmentation, behavioral analytics, and automated response systems to create resilient cyber defense mechanisms. The framework proposed by the National Institute of Standards and Technology in NIST SP 800-207 Zero Trust Architecture serves as a foundational reference for this research.
Introduction
The cybersecurity landscape has evolved dramatically over the past decade. Organizations increasingly rely on distributed infrastructures that include cloud platforms, mobile devices, Internet of Things (IoT) systems, and remote workforce environments. While these technological advancements enhance productivity and scalability, they also introduce significant security challenges.
Traditional security architectures relied heavily on the concept of a trusted internal network protected by firewalls and perimeter defenses. Once users or devices entered the network, they were generally considered trustworthy. However, cyber attackers have adapted their tactics and now frequently exploit compromised credentials, phishing attacks, and insider vulnerabilities to gain access to internal systems.
This shift has rendered perimeter-based security models inadequate. Attackers who bypass the outer defenses can often move laterally within the network with minimal resistance. As a response to this growing threat landscape, cybersecurity experts have introduced the concept of Zero Trust Architecture (ZTA).
Zero Trust is based on the principle “Never Trust, Always Verify.” Instead of assuming that internal users or systems are safe, Zero Trust requires continuous authentication and authorization for every access request. In the context of a Security Operations Center (SOC), Zero Trust provides a comprehensive framework for monitoring, detecting, and responding to cyber threats in real time.
SOC Zero Trust Architecture integrates multiple security technologies including identity and access management, endpoint security, network micro-segmentation, threat intelligence, and automated incident response. Together, these components create a security ecosystem capable of defending modern organizations against advanced cyber attacks.
Evolution of Security Operations Centers
Security Operations Centers serve as the central hub for monitoring and defending an organization’s digital infrastructure. SOC teams analyze security alerts, investigate incidents, and coordinate responses to cyber threats.
Historically, SOC operations focused primarily on network perimeter defenses and signature-based detection mechanisms. Tools such as intrusion detection systems and firewalls played a dominant role in identifying malicious activity.
However, the increasing complexity of modern IT infrastructures has significantly expanded the responsibilities of SOC teams.
Today’s SOC analysts must monitor a wide range of data sources including:
Cloud workloads
Endpoint devices
Network traffic
User authentication logs
Application activity
In this environment, the traditional assumption of network trust no longer holds. Attackers frequently exploit stolen credentials to impersonate legitimate users and bypass traditional defenses.
Zero Trust Architecture fundamentally changes SOC operations by enforcing strict verification for every interaction within the network.
Principles of Zero Trust Architecture
Zero Trust security architecture is built upon several foundational principles that redefine how organizations approach cybersecurity.
Continuous Verification
Every user, device, and application must be authenticated and authorized before accessing resources. Authentication is not a one-time process but occurs continuously throughout the user session.
Identity verification mechanisms may include passwords, biometric authentication, hardware tokens, or multi-factor authentication systems.
Least Privilege Access
Zero Trust enforces the principle of least privilege, ensuring that users only receive the minimum level of access required to perform their tasks. By limiting permissions, organizations reduce the potential damage caused by compromised accounts or insider threats.
Assume Breach
Zero Trust operates under the assumption that attackers may already be present within the network. Rather than focusing solely on preventing intrusion, the architecture emphasizes detection, containment, and rapid response to security incidents.
Micro-Segmentation
Instead of relying on a single large trusted network, Zero Trust divides infrastructure into smaller isolated segments. This prevents attackers from moving laterally across the network if they compromise a system.
These principles collectively create a security model that continuously evaluates risk and enforces strict access controls.
Core Components of SOC Zero Trust Architecture
Implementing Zero Trust within a Security Operations Center requires the integration of several key technologies and operational processes.
Identity and Access Management
Identity management plays a critical role in Zero Trust architecture. Every user must be verified before accessing corporate resources. Modern identity platforms enable organizations to enforce strong authentication policies and monitor suspicious login activity.
Solutions such as Microsoft Entra ID and Okta provide advanced identity security capabilities including multi-factor authentication, conditional access policies, and identity risk assessment.
SOC teams monitor authentication logs to detect anomalies such as impossible travel patterns, repeated login failures, or unauthorized privilege escalation attempts.
Endpoint Security and Device Verification
Endpoints represent one of the most common entry points for cyber attackers. Laptops, mobile devices, and IoT systems frequently connect to corporate environments and may introduce vulnerabilities.
Zero Trust requires continuous verification of device security posture before granting access to resources. Endpoint Detection and Response platforms such as CrowdStrike and SentinelOne monitor endpoint activities and detect malicious behaviour in real time.
These platforms provide SOC analysts with detailed visibility into system processes, file modifications, and suspicious network connections.
Network Micro-Segmentation
Network segmentation is a critical component of Zero Trust architecture. By dividing networks into smaller isolated zones, organizations can limit the potential impact of security breaches.
Zero Trust Network Access solutions allow users to access specific applications without exposing the entire network infrastructure. Security platforms such as Zscaler and Palo Alto Networks provide advanced segmentation and access control capabilities.
This approach significantly reduces the risk of lateral movement within the network.
Security Monitoring and Analytics
Continuous monitoring is essential for detecting cyber threats in real time. Security Information and Event Management systems collect and analyze large volumes of log data from across the organization.
Popular SIEM platforms include Splunk Enterprise Security, IBM QRadar, and Microsoft Sentinel.
These systems enable SOC analysts to correlate events, identify anomalies, and generate alerts when suspicious activities occur.
User and Entity Behavior Analytics (UEBA) further enhances threat detection by identifying unusual patterns in user behavior.
Security Automation and Response
Security Operations Centers often face overwhelming volumes of alerts and security events. Automation helps reduce analyst workload and improves response times.
Security Orchestration, Automation, and Response platforms enable automated workflows that respond to security incidents without manual intervention. Tools such as Cortex XSOAR can automatically isolate compromised devices, block malicious IP addresses, and generate incident reports.
Automation ensures that threats are contained quickly before they escalate into larger security incidents.
Benefits of SOC Zero Trust Architecture
Organizations implementing Zero Trust architectures experience several significant advantages.
First, Zero Trust significantly reduces the attack surface by eliminating implicit trust within the network. Even if attackers obtain valid credentials, additional verification steps prevent unauthorized access.
Second, network segmentation prevents attackers from moving laterally across systems. Compromising a single endpoint does not provide access to the entire infrastructure.
Third, continuous monitoring improves threat detection capabilities. SOC analysts gain visibility into every user activity, device connection, and network transaction.
Finally, Zero Trust architectures support regulatory compliance by enforcing strict access controls and maintaining detailed audit logs.
Implementation Challenges
Despite its advantages, implementing Zero Trust architecture presents several challenges.
Many organizations rely on legacy systems that were not designed to support modern authentication mechanisms. Integrating these systems into a Zero Trust environment requires careful planning and modernization.
Another challenge involves managing the complexity of security policies. Large organizations may require thousands of access rules to manage different user roles, applications, and devices.
Additionally, organizations must balance security with user experience. Excessive authentication requirements can create friction for employees and reduce productivity.
Successful Zero Trust implementations therefore require strong governance, clear security policies, and collaboration between IT and security teams.
Future of SOC Zero Trust Architecture
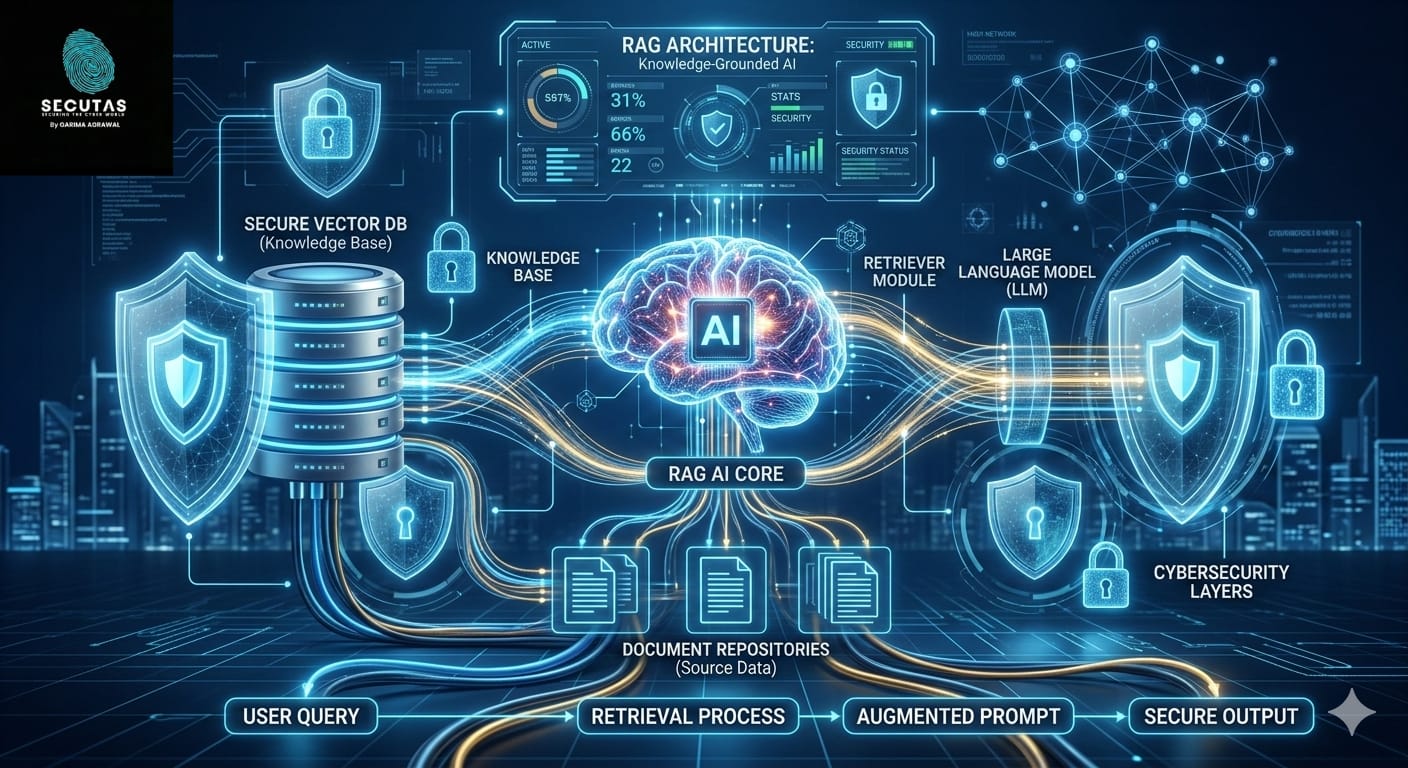
The future of cybersecurity operations will likely be defined by the convergence of Zero Trust architecture with artificial intelligence and machine learning technologies.
AI-powered security analytics can process vast volumes of security data and identify subtle patterns that human analysts may overlook. These capabilities enable earlier detection of advanced persistent threats and insider attacks.
Automation will also play an increasingly important role in SOC operations. Autonomous security systems may eventually detect, investigate, and respond to cyber threats with minimal human intervention.
As organizations continue to adopt cloud computing and remote work environments, Zero Trust architecture will become the foundation of modern cybersecurity strategies.
Conclusion
SOC Zero Trust Architecture represents a fundamental transformation in how organizations approach cybersecurity. By eliminating implicit trust and continuously verifying every access request, Zero Trust provides a powerful framework for protecting modern digital infrastructures.
Through the integration of identity management, endpoint security, network segmentation, behavioral analytics, and automated response systems, Zero Trust enables Security Operations Centers to detect and respond to threats more effectively.
As cyber threats continue to evolve, organizations must adopt proactive security strategies that prioritize visibility, verification, and rapid response. Zero Trust SOC architecture offers a comprehensive approach to achieving these goals and ensuring long-term cybersecurity resilience


Leave a Reply