In today’s digital ecosystem, Application Programming Interfaces (APIs) have become the backbone of modern software architectures. APIs enable communication between applications, services, mobile devices, and cloud platforms. From mobile banking apps to e-commerce platforms and cloud-native microservices, APIs power nearly every interaction in the digital world. However, as organizations increasingly rely on APIs to enable functionality and connectivity, these interfaces also become one of the most attractive attack surfaces for cybercriminals.
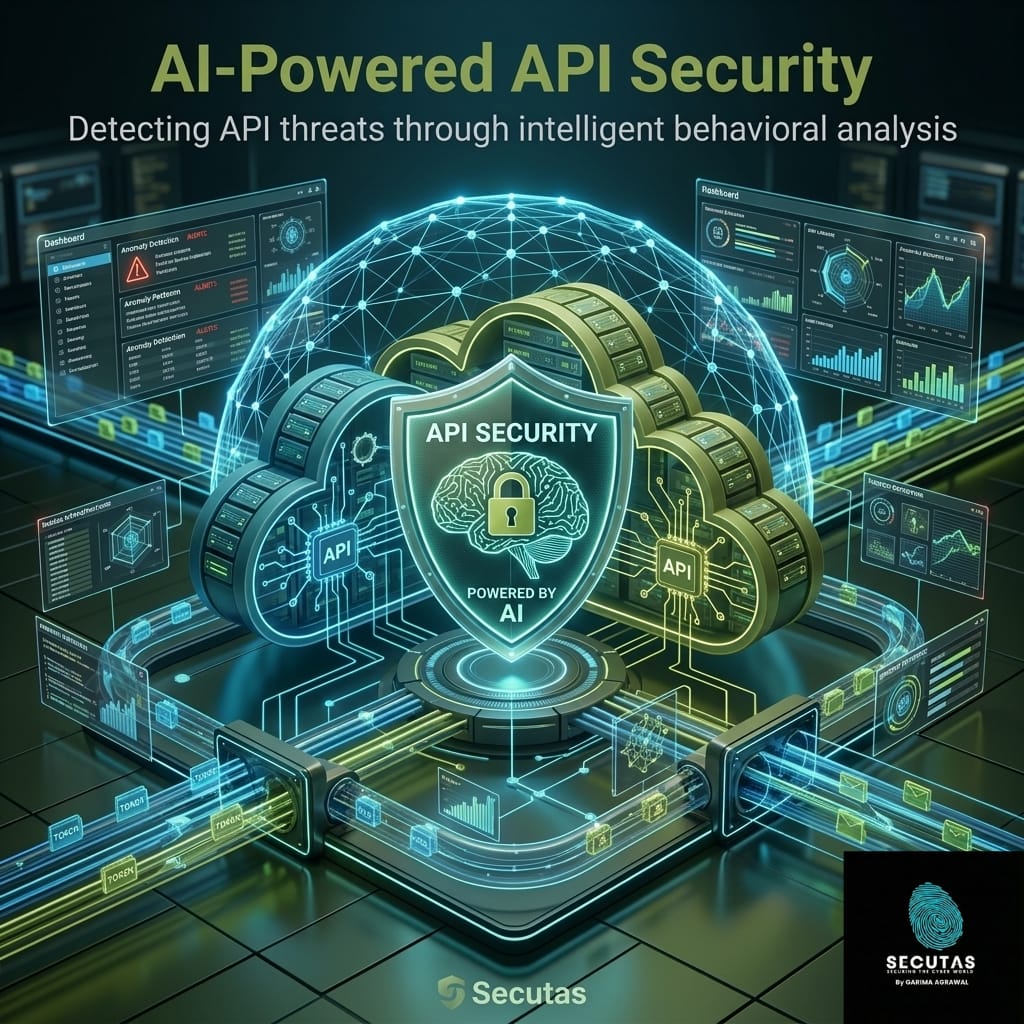
With the rapid adoption of cloud computing platforms such as Amazon Web Services, Microsoft Azure, and Google Cloud Platform, organizations are deploying hundreds or even thousands of APIs to connect services and manage data. Managing and securing these APIs using traditional security methods alone is no longer sufficient. This is where Artificial Intelligence (AI) is transforming the landscape of API security. By analyzing vast amounts of traffic data and behavioral patterns, AI-powered systems enable organizations to detect threats earlier, respond faster, and build more resilient cloud security architectures.
The Growing Importance of API Security
APIs act as gateways to applications and data. They allow different software components to exchange information, automate processes, and integrate services across platforms. For example, when a user logs into a mobile banking application, the app communicates with backend servers through APIs to authenticate the user, retrieve account data, and process transactions.
Because APIs directly expose application logic and data, attackers often target them to gain unauthorized access, manipulate transactions, or extract sensitive information. According to security researchers, many modern cyberattacks exploit poorly secured APIs rather than attacking the infrastructure directly.
The risks associated with insecure APIs are highlighted by the Open Worldwide Application Security Project through its OWASP API Security Top 10, which identifies the most critical API vulnerabilities. These include broken authentication, excessive data exposure, lack of rate limiting, and improper authorization checks. As organizations scale their digital services in cloud environments, the number of APIs continues to grow, making manual monitoring increasingly difficult.
Challenges of Securing APIs in the Cloud
Cloud-native architectures introduce new complexities for API security. Unlike traditional monolithic systems, cloud environments rely heavily on microservices architectures, where multiple services communicate with each other through APIs. Each microservice may expose its own API endpoints, creating a distributed network of interconnected components.
This architecture improves scalability and flexibility, but it also increases the attack surface. Security teams must monitor a large volume of API requests, authentication events, data transfers, and user interactions across multiple services and environments. Traditional rule-based security tools often struggle to keep up with this complexity.
Another challenge is the dynamic nature of cloud environments. APIs are frequently updated, scaled, and integrated with third-party services. New endpoints may be deployed quickly as part of DevOps workflows, sometimes without adequate security testing. As a result, organizations may have shadow APIs—untracked or undocumented endpoints that can become entry points for attackers.
To effectively secure cloud APIs, organizations need intelligent systems capable of analyzing behavior patterns, detecting anomalies, and responding to threats in real time. This is where artificial intelligence provides a powerful advantage.
How Artificial Intelligence Enhances API Security
Artificial intelligence introduces a new approach to cybersecurity by enabling systems to learn patterns, identify anomalies, and automate threat detection. Instead of relying solely on predefined rules or signatures, AI models analyze historical data and real-time activity to understand what normal behavior looks like.
When applied to API security, AI systems continuously monitor API traffic and identify unusual patterns that may indicate malicious activity. For example, AI algorithms can analyze factors such as request frequency, geographic access patterns, authentication attempts, and data transfer volumes.
If a user suddenly begins sending thousands of API requests per minute from an unfamiliar location, an AI system can flag this behavior as suspicious. Similarly, if an API endpoint begins receiving requests outside its normal usage pattern, the system can generate alerts or trigger automated responses.
This ability to learn and adapt to evolving threats makes AI particularly valuable in cloud environments where attack patterns constantly change.
Behavioral Analytics and Anomaly Detection
One of the most effective applications of AI in API security is behavioral analytics. Machine learning models establish baselines for normal user and application behavior by analyzing historical API traffic data. These models learn patterns such as typical login times, request frequencies, data access patterns, and service interactions.
Once a baseline is established, the system continuously monitors real-time activity and compares it to expected patterns. When deviations occur, the system identifies them as anomalies.
For example, if a legitimate user typically accesses an API from a specific geographic region during business hours, a sudden login attempt from another country at an unusual time may trigger an alert. Similarly, if an API endpoint designed for limited queries begins receiving large volumes of requests, the system may detect a potential bot attack or data scraping attempt.
AI-based anomaly detection is particularly useful for identifying zero-day attacks and unknown threats, which may not match existing attack signatures.
Detecting Automated Attacks and Bot Activity
APIs are frequently targeted by automated attacks. Bots can attempt to exploit APIs through credential stuffing, brute-force login attempts, or automated data scraping. These attacks often generate massive volumes of traffic that can overwhelm traditional monitoring systems.
AI-powered security platforms can identify bot behavior by analyzing request timing, behavioral patterns, and interaction characteristics. Unlike human users, bots often generate requests with consistent timing intervals or unusual interaction sequences.
By analyzing these patterns, AI systems can distinguish between legitimate user activity and automated attack behavior. When malicious bots are detected, security tools can implement countermeasures such as blocking suspicious IP addresses, enforcing rate limits, or requiring additional authentication steps.
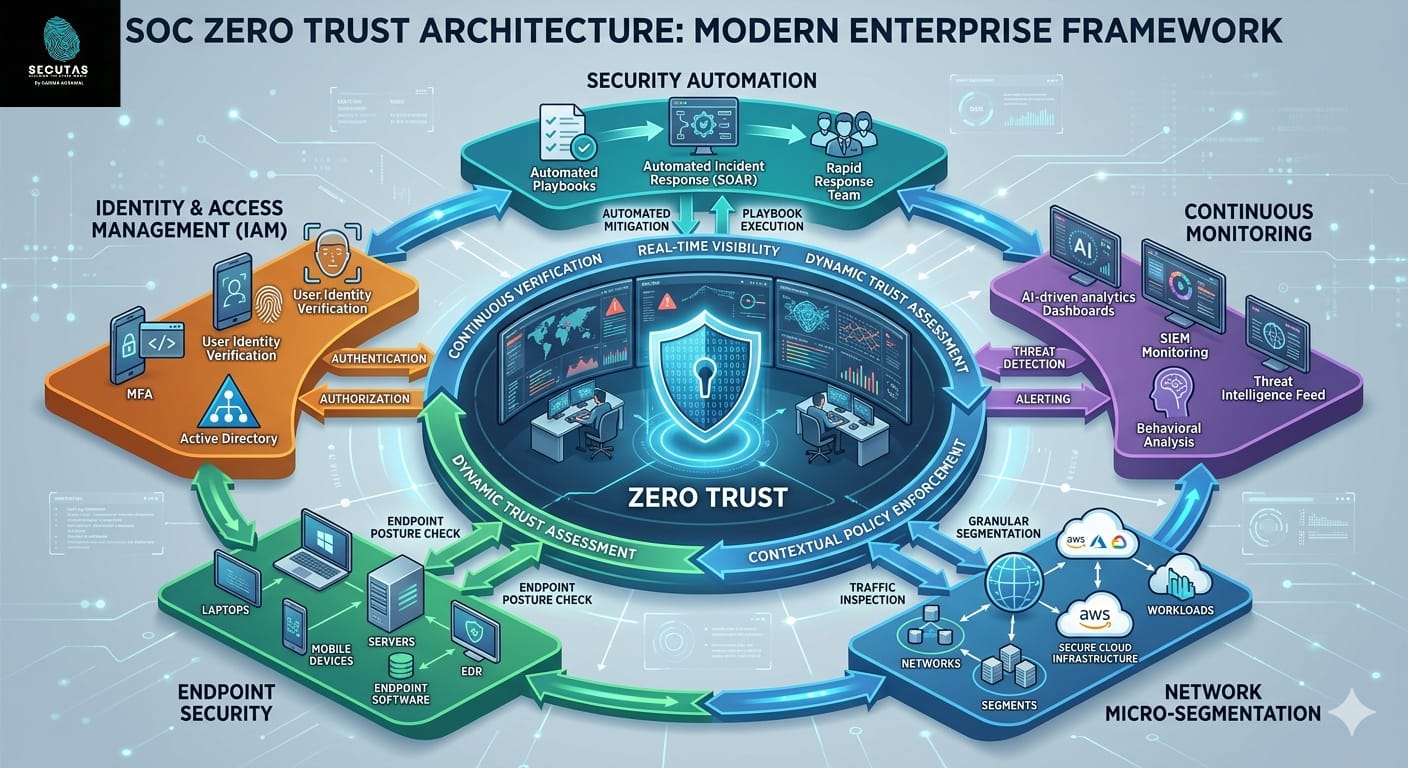
Integrating AI with Security Operations
AI-based API security becomes even more powerful when integrated with modern Security Operations Center (SOC) technologies. Security monitoring platforms such as SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) collect and analyze security data across an organization’s infrastructure.
When AI-driven detection systems identify suspicious API activity, they can send alerts to SIEM platforms for further analysis. SOAR platforms can then automate response actions such as isolating compromised accounts, blocking malicious requests, or triggering incident response workflows.
This integration enables organizations to move toward automated security operations, where threats are detected and mitigated with minimal manual intervention. Security analysts can focus on investigating complex incidents rather than manually reviewing thousands of alerts.
AI Techniques Used in API Security
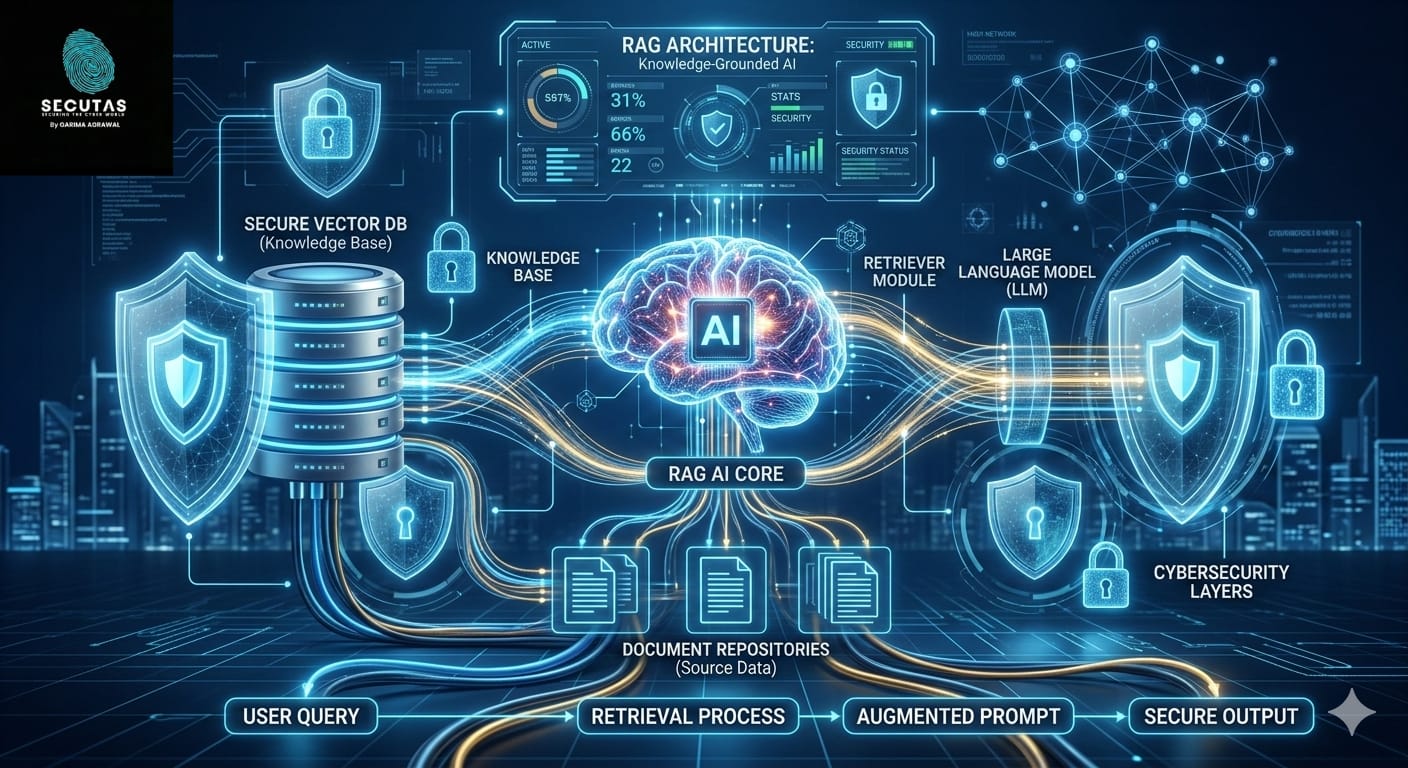
Several AI and machine learning techniques are commonly used to secure APIs in cloud environments. Supervised learning models are often trained to classify API requests as legitimate or malicious based on labeled training data. These models can identify known attack patterns and prevent common threats.
Unsupervised learning methods, such as clustering and anomaly detection algorithms, are particularly valuable for detecting unknown threats. These algorithms analyze data patterns without predefined labels and identify deviations from normal behavior.
Deep learning models may also be used to analyze complex patterns in large datasets, such as sequences of API calls or multi-stage attack behaviors. In addition, graph analytics techniques can map relationships between users, APIs, and services to detect suspicious interaction patterns.
By combining multiple AI techniques, organizations can build multi-layered defense systems capable of detecting a wide range of threats.
Benefits of AI-Powered API Security
Implementing AI-driven API security provides several advantages for modern organizations. One of the most significant benefits is the ability to detect threats in real time. AI systems continuously analyze incoming API traffic and identify suspicious patterns before attacks escalate.
Another advantage is improved scalability. Cloud environments generate enormous volumes of data, and AI systems can process this data far more efficiently than manual analysis. This allows security teams to monitor large infrastructures without overwhelming human analysts.
AI also helps reduce false positives, which are a common challenge in traditional security monitoring. By understanding behavioral context, AI systems can differentiate between legitimate anomalies and actual threats, reducing unnecessary alerts.
Furthermore, AI enables organizations to implement adaptive security strategies. As threat landscapes evolve, machine learning models can update their understanding of normal behavior and adjust detection mechanisms accordingly.
Best Practices for Implementing AI-Based API Security
While AI provides powerful capabilities, effective API security still requires a comprehensive security strategy. Organizations should begin by implementing strong authentication and authorization mechanisms, such as OAuth tokens and multi-factor authentication. These controls help ensure that only authorized users can access APIs.
API gateways and web application firewalls should also be deployed to filter and manage API traffic. These systems can enforce rate limits, validate input data, and block suspicious requests before they reach backend services.
Logging and monitoring are equally important. Organizations should collect detailed logs of API requests, authentication events, and system interactions. These logs provide the data required for training AI models and conducting security analysis.
Finally, security teams should adopt a DevSecOps approach, integrating security practices into the development lifecycle. Regular security testing, vulnerability assessments, and code reviews help identify potential API vulnerabilities before deployment.
The Future of AI and API Security
As digital ecosystems continue to evolve, the role of AI in cybersecurity will become increasingly significant. Future AI-driven security systems may incorporate advanced capabilities such as predictive threat analysis, automated vulnerability discovery, and autonomous incident response.
Emerging technologies such as AI-powered security agents may monitor entire cloud environments, continuously analyzing system behavior and automatically applying defensive measures. These intelligent systems could significantly reduce response times and help organizations stay ahead of sophisticated attackers.
However, the rise of AI in cybersecurity also introduces new challenges. Attackers may attempt to manipulate AI systems through adversarial techniques or data poisoning attacks. As a result, securing AI models themselves will become an important aspect of cybersecurity strategy.
Strengthening API Security Through Intelligent Defense
API security has become a critical priority for organizations operating in cloud environments. As digital services expand and application architectures grow more complex, traditional security methods alone are no longer sufficient. Artificial intelligence provides a powerful tool for analyzing behaviour, detecting anomalies, and responding to threats in real time.
By combining AI with strong security governance, modern security operations, and cloud-native protections, organizations can build resilient and adaptive security architectures capable of defending against evolving threats.
At Secutas, the focus is on exploring how emerging technologies such as artificial intelligence, behavioral analytics, and intelligent threat detection can strengthen cybersecurity practices. As organizations move toward AI-driven security operations, the integration of AI-powered API protection in cloud environments will play a crucial role in safeguarding the digital infrastructure of the future.


Leave a Reply