Understanding the STRIDE Threat Modeling Framework
In today’s hyperconnected digital landscape, security can no longer be treated as an afterthought. Applications are increasingly complex, distributed across cloud environments, APIs, microservices, and third-party integrations. As systems grow in complexity, so do the potential attack surfaces. Threat modeling provides a structured way to anticipate, identify, and mitigate security risks before they are exploited. Among the various threat modeling approaches available, the STRIDE Threat Modeling Framework stands out for its simplicity, clarity, and practical relevance.
STRIDE is a systematic methodology designed to help security professionals, architects, and developers think like attackers while designing or reviewing systems. Instead of reacting to vulnerabilities after deployment, STRIDE encourages proactive identification of threats during the design phase. This proactive mindset significantly reduces the cost and impact of security incidents while improving the overall robustness of software systems.
Origins and Purpose of STRIDE
The STRIDE framework was introduced by Microsoft as part of its Secure Development Lifecycle (SDL). The primary goal was to give development teams a repeatable and easy-to-understand method for identifying common categories of threats. Rather than focusing on specific exploits or vulnerabilities, STRIDE classifies threats based on the fundamental ways a system can be attacked.
This abstraction is one of STRIDE’s greatest strengths. By categorizing threats into six well-defined classes, the framework allows teams to systematically analyze each component of a system and ask targeted security questions. The result is a more complete threat analysis that is less dependent on individual expertise and more reliant on structured reasoning.
What Does STRIDE Stand For?
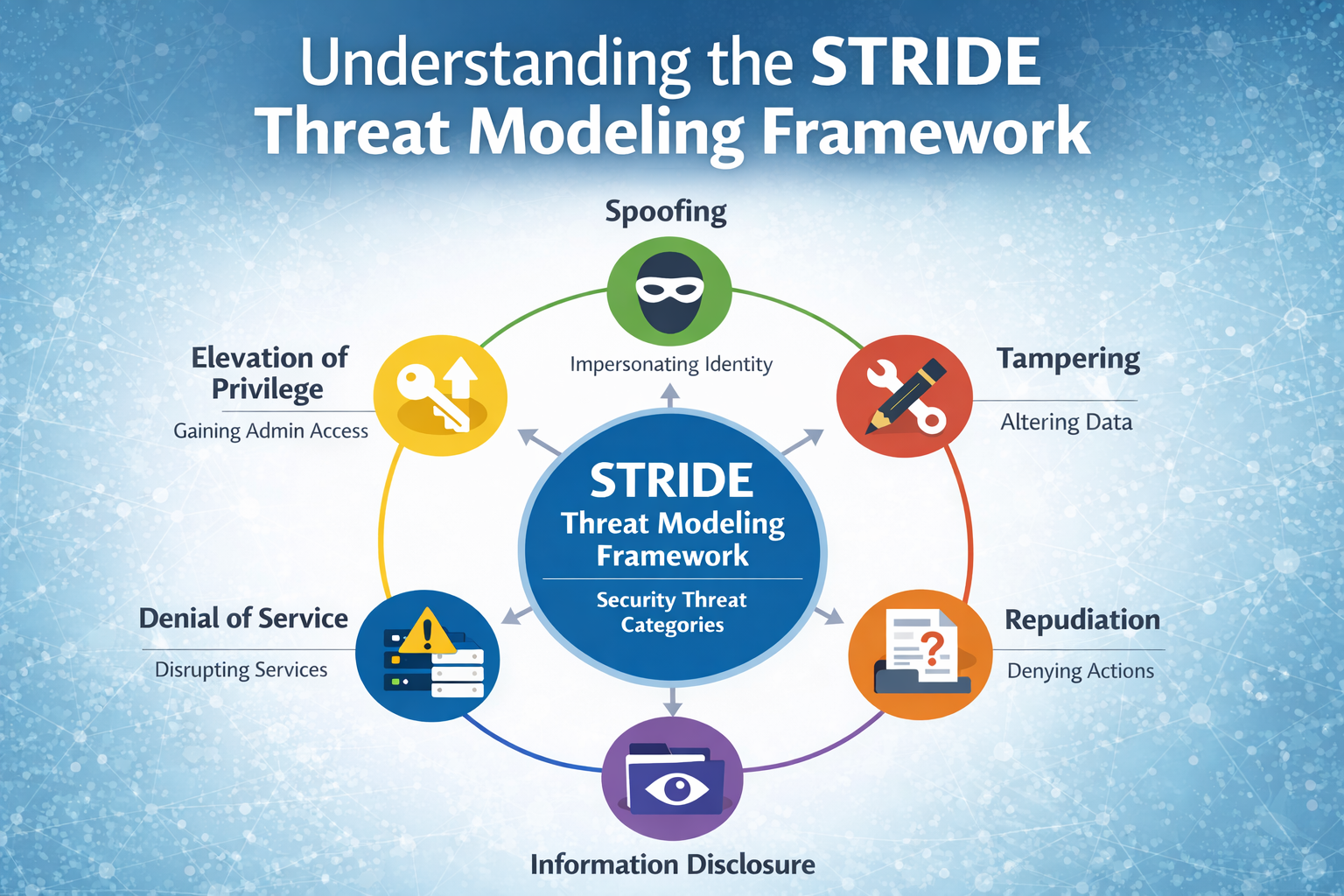
STRIDE is an acronym representing six categories of security threats:
- Spoofing
- Tampering
- Repudiation
- Information Disclosure
- Denial of Service
- Elevation of Privilege
Each category corresponds to a violation of a fundamental security property such as authentication, integrity, non-repudiation, confidentiality, availability, or authorization. By mapping threats to these properties, STRIDE ensures comprehensive coverage of the most critical security concerns.
Spoofing: Attacks on Identity
Spoofing refers to threats where an attacker pretends to be someone or something else. This typically involves compromising authentication mechanisms to impersonate legitimate users, services, or systems. Common examples include credential theft, session hijacking, and impersonation of services using forged certificates or tokens.
Spoofing attacks undermine trust within a system. If a system cannot reliably verify identities, all subsequent authorization and auditing controls become ineffective. STRIDE encourages teams to ask questions such as: How is identity established? Are credentials protected in transit and at rest? Are multi-factor authentication and strong cryptographic mechanisms in place?
Mitigations against spoofing often include robust authentication protocols, secure password storage, token expiration policies, and mutual authentication between services.
Tampering: Attacks on Integrity
Tampering threats involve unauthorized modification of data, whether at rest, in transit, or during processing. This can include altering database records, modifying configuration files, injecting malicious payloads, or manipulating API requests.
The impact of tampering can range from subtle data corruption to complete system compromise. STRIDE prompts teams to examine where data integrity could be violated and what controls exist to prevent or detect such changes. Questions often focus on whether data is digitally signed, whether secure communication channels are used, and whether access controls are properly enforced.
Effective mitigations include cryptographic hashing, digital signatures, secure transport protocols like TLS, and strict input validation. Logging and monitoring also play a critical role in detecting tampering attempts.
Repudiation: Attacks on Accountability
Repudiation threats arise when a user or system can deny having performed an action without the ability for the system to prove otherwise. In environments where accountability is critical—such as financial systems, healthcare platforms, or enterprise applications—repudiation poses a serious risk.
STRIDE encourages teams to think about how actions are recorded and whether logs can be trusted. Are logs tamper-resistant? Do they capture sufficient context such as timestamps, user identities, and transaction details? Can logs be correlated across systems?
Mitigations typically involve secure, centralized logging, digital signatures on transactions, time synchronization, and proper audit trail management. Non-repudiation is especially important for compliance and forensic investigations following a security incident.
Information Disclosure: Attacks on Confidentiality
Information disclosure threats involve the exposure of sensitive data to unauthorized parties. This could include personal data, credentials, intellectual property, or system configuration details. Such disclosures can occur through insecure storage, weak encryption, verbose error messages, or misconfigured access controls.
STRIDE highlights the need to classify data and understand where sensitive information flows within a system. Teams are encouraged to identify where data is stored, transmitted, and processed, and to evaluate whether confidentiality controls are sufficient at each stage.
Mitigation strategies include encryption at rest and in transit, data minimization, role-based access control, and careful error handling. Regular security testing and configuration reviews are also essential to prevent accidental data exposure.
Denial of Service: Attacks on Availability
Denial of Service (DoS) threats aim to make a system unavailable to its intended users. This can be achieved through resource exhaustion, traffic flooding, logic abuse, or exploitation of performance bottlenecks. While some DoS attacks are large-scale and external, others can be subtle and originate from within the system.
STRIDE prompts teams to consider how resilient their system is under stress. What happens if a component fails or is overwhelmed? Are there rate limits, timeouts, and circuit breakers in place? Is the system designed to degrade gracefully?
Mitigations include load balancing, rate limiting, resource quotas, redundancy, and robust monitoring. Cloud-native architectures often provide built-in tools to help address availability concerns, but these must be correctly configured to be effective.
Elevation of Privilege: Attacks on Authorization
Elevation of Privilege (EoP) threats occur when an attacker gains higher permissions than intended. This often results from flaws in authorization logic, misconfigured roles, or exploitable software vulnerabilities. EoP attacks are particularly dangerous because they can lead to full system compromise.
STRIDE encourages a close examination of privilege boundaries within a system. Are roles clearly defined? Is the principle of least privilege enforced? Are administrative functions adequately protected?
Common mitigations include strong authorization checks, separation of duties, regular permission reviews, and secure coding practices. Defense-in-depth is especially important here, as a single failure should not result in unrestricted access.
Applying STRIDE in Practice
In practice, STRIDE is often used alongside system diagrams such as data flow diagrams (DFDs). Each component—processes, data stores, data flows, and external entities—is analyzed against all six STRIDE categories. This structured walkthrough helps ensure that no major threat class is overlooked.
STRIDE is frequently used in conjunction with other security methodologies and standards, including guidance from organizations such as OWASP. While STRIDE focuses on threat categories, complementary approaches can help prioritize risks and map them to real-world vulnerabilities.
Strengths and Limitations of STRIDE
One of STRIDE’s key strengths is its accessibility. It does not require deep security expertise to get started, making it suitable for cross-functional teams. It also scales well, from small applications to large enterprise systems.
However, STRIDE is not without limitations. It does not inherently provide risk scoring or prioritization, nor does it account for business impact on its own. As a result, many teams combine STRIDE with risk assessment frameworks or attack modeling techniques to guide remediation efforts.
Conclusion
The STRIDE Threat Modeling Framework remains a cornerstone of modern application security due to its clarity, structure, and practical focus. By categorizing threats into six fundamental classes, STRIDE helps teams systematically identify and address security risks early in the development lifecycle.
In an era where security breaches can have far-reaching consequences, adopting a proactive and structured approach to threat modeling is no longer optional. STRIDE provides a proven foundation for building more secure systems, fostering a security-first mindset, and ultimately delivering software that users can trust.


Leave a Reply